Continuation of security verification results of the proposed scheme... | Download Scientific Diagram
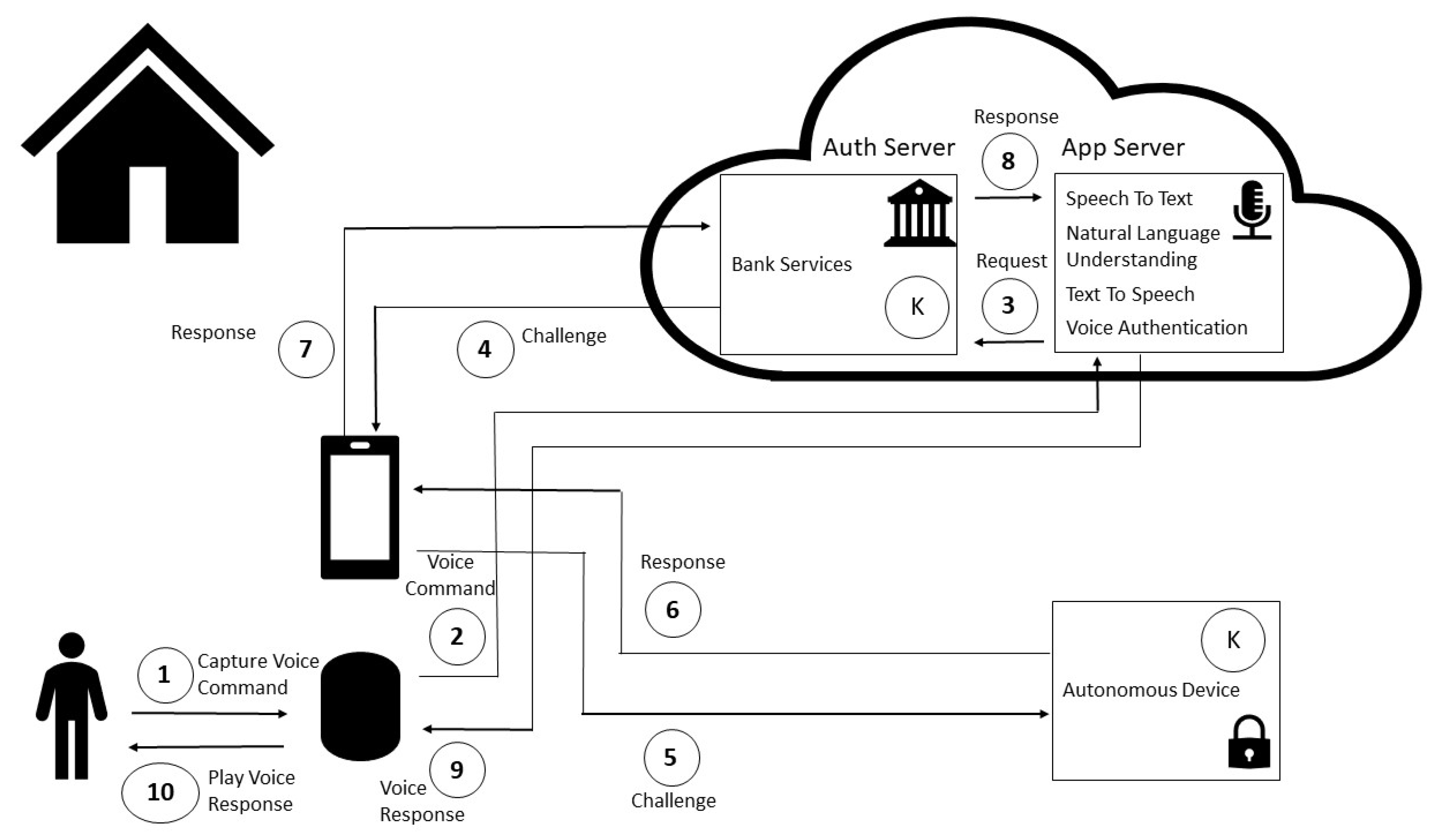
Sensors | Free Full-Text | Non-Invasive Challenge Response Authentication for Voice Transactions with Smart Home Behavior | HTML

A lightweight authentication protocol for IoT‐based cloud environment - Zargar - - International Journal of Communication Systems - Wiley Online Library

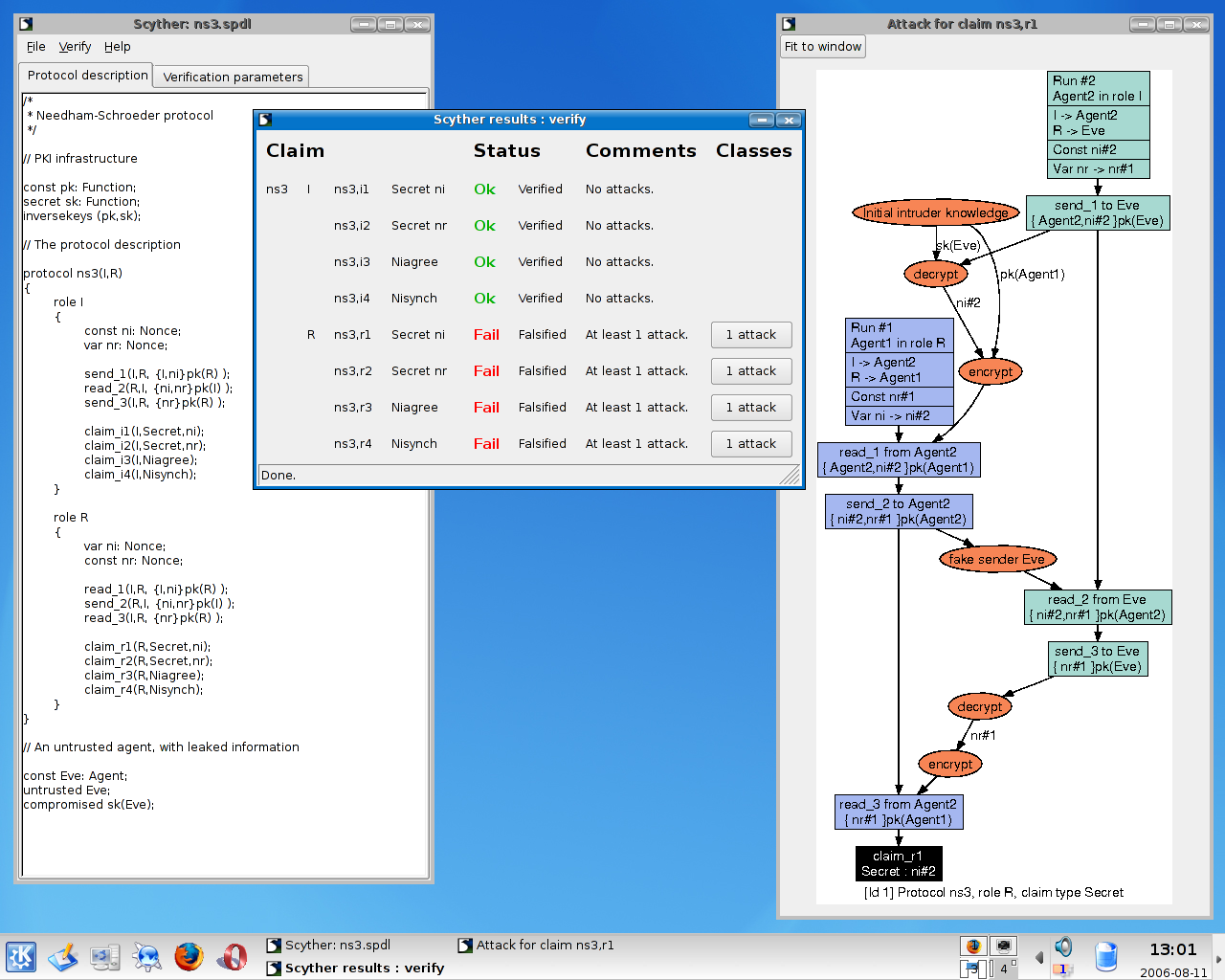
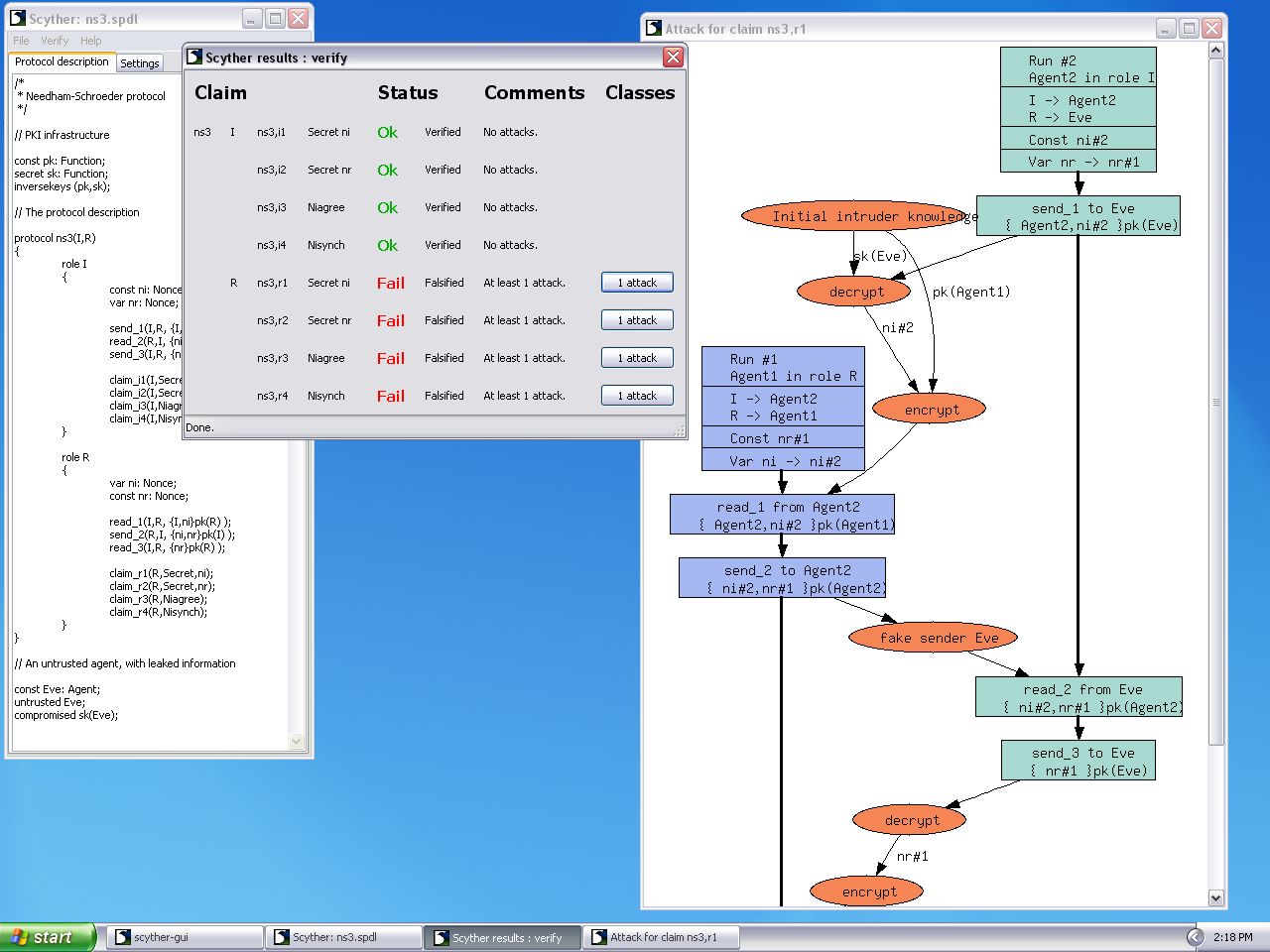
scyther tool installation on windows. Scyther model checker installation on windows OS. Formal Verif - YouTube

Security verification results of the proposed scheme using the Scyther tool | Download Scientific Diagram
GitHub - binhnguyen1984/scyther-abstraction: The Scyther-abstraction Tool for the symbolic analysis of security protocols

Security verification results of the Khemissa et al.'s protocol using... | Download Scientific Diagram

Scyther (Formal Verification Tool) Installation on Windows #Scyther #Formalverification #Windows - YouTube

Sensors | Free Full-Text | IMSC-EIoTD: Identity Management and Secure Communication for Edge IoT Devices | HTML

Security verification results of the Khemissa et al.'s protocol using... | Download Scientific Diagram


![Scyther Manual - [PDF Document] Scyther Manual - [PDF Document]](https://demo.staticloud.net/img/full/reader018/html5/20191105/55cf8f2a550346703b998e16/bg1.png)

![Scyther Manual - [PDF Document] Scyther Manual - [PDF Document]](https://cdn.cupdf.com/img/1200x630/reader018/image/20191105/55cf8f2a550346703b998e16.png)